IoT security awareness is not what it should be yet as research by Trend Micro, conducted by Vanson Bourne shows. Yet, the issue seems to be larger and still about cybersecurity awareness and training in general too if we look at other research. Some takeaways, lessons from GDPR awareness and analyst advice with a focus on IIoT.
IoT security is – and will remain – a major challenge for pretty much all products, solutions, deployments and initiatives where IoT technologies are involved one way or the other: from consumer-oriented applications and things (where we tackled the need of awareness several years ago) to Industrial IoT (IIoT).
There are obviously various ways to enhance security. However, without IoT security awareness and a – good – strategy (you can’t plan and define a strategy without awareness) you get nowhere.
Of course, cybersecurity is – and, again, remains – a key issue concern for all technology- and data-related activities. In other words: for a lot of what organizations do nowadays. And how else could it be? When data is the glue (and personal data the goldmine – for hackers too) the ‘bad guys’ continue to come up with new ways of exploiting vulnerabilities and other means to achieve their goals.
Yet, with IoT security – both in the Industrial IoT environments of Industry 4.0, industrial control systems and SCADA systems as in less industrial environments, the challenges are quite different.
Still, there are also many common lessons – and some are, or at least should be – relatively obvious by now. And, as tends to be the case in security overall, the basics lack far too often, even if IoT security technology maturity is on the rise in, among others, industrial settings as mentioned in an article on IoT security forecasts and trends. That’s where this post about IoT security awareness comes in.
IoT security awareness – the habits of employees
There are two direct ‘triggers’ why we wrote this article on IoT security awareness with a focus on IIoT, though the overarching reason is the increasing importance of IoT and the fact that IoT security is still that big concern which slows down adoption and is one of the major de facto risk factors for so many industrial use cases and initiatives.
The first reason – or trigger – are findings from SailPoint’s 2018 Market Pulse Survey (released on November 12, 2018), showing that the security-related habits of employees seem to be worsening again. 75% of employees admitted to reusing passwords across accounts, for example. In 2014 this was “only” the case for 56% of responding employees. While this might seem unrelated to IoT security awareness it partially is. The report made us wonder what happened with awareness of risks regarding security overall.
Let’s explain. You might remember the existence of this personal data protection framework called GDPR. What was the first step on the journey towards compliance? GDPR awareness.
This doesn’t just mean you need to know GDPR exists of course. It also means being aware of the risks for your organization (which includes knowing and mapping them), making executives aware, training your people (who need to be aware too) on how to deal with personal data and of course reminding them what to do and what not to do when it boils down to security. So, it struck us as kind of weird that there are “worrying signs” in that sense and that, as SailPoint puts it, “when it comes to employees’ cybersecurity habits, history repeats itself”.
It’s not so much the ‘history repeats itself part’ but the ‘why now?’ question that pops up – and can’t we learn from the lessons we learned from GDPR? There are more calls for regulation, data protection and privacy and there is most certainly more attention for security, also regarding IoT. Just as compliance requires an ongoing effort, so does creating awareness about security on an executive level, getting executive guidance and training those that needs to be trained, depending on their role. By the way, according to the SailPoint survey, 66% of respondents don’t know what the GDPR is so that explains quite a bit.
The overlap between compliance and regulations awareness and IoT security awareness becomes clearer in an article on IoT security spending for the period until 2021 where we cited Gartner. The company had predicted that by 2021, regulatory compliance will become the prime influencer for IoT security. Moreover, there are arguments to look at IoT security awareness as we prepared for GDPR. IoT security is complex and involves different stakeholders of which some don’t have too much experience with the IT side of security. Furthermore, these stakeholders also include various partners. GDPR compliance by definition was a holistic exercise that inevitably touched upon the broader ecosystem of what happens with personal data. Simply put: you needed to involve data processors, various departments (on top of IT and management HR, marketing, you name it) and of course partners to get it done. That seems like an ‘ecosystem’ process – at least if you do it right. And aren’t ecosystems precisely what we talk about in IoT and IoT security as well?
The IoT security awareness silo challenge and IIoT security awareness
Obviously one of the many challenges that stands in the way of what one could call a more holistic approach regarding security awareness is that of the eternal silos, in IoT security awareness too, albeit more on the level of culture, thinking and the skills and mindsets in quite different groups.
Industrial IoT is still about IT and OT. While the risks in IT and OT overlap, they are indeed different. Processes, systems, there are key differences. However, when we speak about IoT security awareness we really speak about culture and tradition. It’s not a secret that IT and OT convergence is at least a matter of people as it is of technologies.

While Gartner dispels the myth that OT and IIoT can use IT methodologies to assess risk and threats, the company also says that “IT and OT cultures are not incompatible, but require executive guidance to realize initial alignment”. And of course we see ever more IT protocols in OT and beyond as we move to this IIoT and IP world where cybersecurity is evolving into a single organism as Gartner adds.
Network security is not the same as training staff (with the necessary guidelines and rules that must be respected by employees and be part of the ‘contract’) on the usage of the apps and devices they also use for work, the list goes on. According to Gartner (and the mentioned post) most IoT security implementations have happened at the level of the business unit whereby IT does get involved but not sufficiently. That shouldn’t come as a surprise but there you have it: alignment, silos, leaving out key stakeholders, it all overlaps.
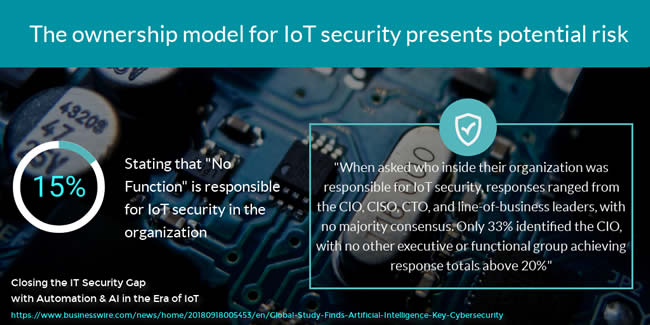
And it gets even worse when you start looking at responsibility. As global research conducted by the Ponemon Institute on behalf of Aruba stated: “Even the ownership model for IoT security presents potential risk” – and how else could it be? When asking who was responsible in the organization for IoT security the answers were very diverse, ranging from “the CIO, CISO, CTO, and line-of-business leaders, with no majority consensus. Only 33 percent identified the CIO, with no other executive or functional group achieving response totals above 20 percent”.
Yet the big surprise (not that big really) was that “No Function” was the third-highest answer with 15 percent of respondents).
This brings us to the second reason or trigger for this IoT security awareness post: the Trend Micro report, announced on November 19, 2018, which focuses on IT execs.
Our main focus is IIoT. This is also related with another announcement from Trend Micro, the cybersecurity firm and industrial communications/networking company Moxa together have executed a letter of intent relating to the formation of a joint-venture corporation: TXOne Networks. It will focus on the security needs present in IIoT environments, “including smart manufacturing, smart city, smart energy and more”.
The focus on Industrial IoT isn’t a coincidence of course since, as the past has shown, the impact of breaches and attacks can be really high here (and the biggest IoT spenders are still industries such as manufacturing). To quote IDC from an article on cybersecurity risks, solutions and evolutions in IIoT, “greater connectivity with operational technology exposes operational teams to the types of attacks that IT teams are used to seeing, but with even higher stakes”.
Moreover, it doesn’t look as if the immediate future will be better, bringing us to another recent report. Earlier in November Texas-based Forcepoint emphasized that “…the possibility of disruption in manufacturing and similar industries makes the threat all the more serious…Meltdown and Spectre have given attackers a way to target hardware vulnerabilities—cloud infrastructure may be next”. One of the other topics that we could add to part of the solutions: edge computing. Yet, that’s for another story since part of the solutions on top of the human, cultural, organizational and strategic ones, to tackle IoT security of course include technologies with edge and certainly artificial intelligence, to name a few.
IoT security awareness – also a matter of prioritization and identifying the weakest links
Back to Trend Micro. So, according to the company there is a major lack of IoT security awareness. Trend Micro found that a large majority of respondents (86%) believe their organization needs to improve its awareness of IoT threats.
The research, conducted by Vanson Bourne, is based on a poll of 1,150 IT and security leaders. And while in this scope we can see IoT security awareness more as an issue for IT, executives and leadership, we can certainly see it in a context of a broader approach of awareness AND training as well.
It’s kicking in an open door when we say that the weakest link in security – and in IoT security – is human. It isn’t any different in industrial environments. In a somewhat older article on cybersecurity on the plant floor, password-related and human challenges were among the risks regarding the weakest link on that plant floor, the human-machine interface systems (HMI/SCADA software). This is just one of many examples.
Sure, there are many vendor-related aspects as well (e.g. slow patching in that HMI context) and it’s key to select those vendors that have the ecosystems in place ensuring the proper IoT security. Yet, the other way around organizations of course should then work in a less ad hoc way as Gartner also stated. Here the human element plays a key role too of course.
Anyway, this post only scratches the surface of IoT and IIoT security and the main aim is to point out those IoT security awareness issues and to emphasize the need to address them, perhaps in a more holistic and collaborative way, with those GDPR lessons in mind. So, a quick look at some findings from the mentioned Trend Micro research.
We keep saying that for most companies IoT is still relatively new but the fact that 37% of respondents claimed they are not always able to define their security needs before implementing IoT solutions is clearly a point that deserves attention.
The actions to take really are in this takeaway from the research: involve IT, security, the ecosystem around the solution etc. from the start on. And that means IoT security awareness too: what are the issues and what to do next. Again, just as with a typical GDPR compliance plan.
Prioritization is another topic. As Trend Micro puts it: “To protect against IoT security attacks, more than 50 percent of surveyed IT and security decision makers reported they prioritize a few key capabilities in their security solutions”.
Referring to the previously mentioned Gartner research: the company pointed out that through 2020, the biggest inhibitor to growth for IoT security will come from a lack of prioritization and implementation of security best practices and tools in IoT initiative planning.
So, all in all, not that many surprises in other words but, still, time to act. Trend Micro: “A lack of IoT security awareness leaves companies increasingly exposed to potentially damaging cyberattacks. According to the survey, current attacks are targeting office devices most, followed by manufacturing and the supply chain. When an attacker compromises these devices, they can also gain access to the greater corporate network to conduct even more damaging attacks”.
Trend Micro recommends a strong network defense approach to ensure IoT devices do not add security risk at any part of a corporate network.
A final note on awareness: the Trend Micro report doesn’t exactly “define” what IoT security awareness is but you can derive that from the findings. Yet, if we agree that we see it in the described sense of GDPR awareness (knowing the risks or being “aware” of them, map, analyze, prioritize, make a plan of attack, align your teams, train and create the needed awareness, insights and so on) ultimately the rest is a matter of getting it done (you already gathered all stakeholders when mapping all risks), monitoring and continue as security is never-ending and the human factor remains the key challenge. Food for thought.

