In our overview of (evolutions in) the Industrial Internet of Things (IIoT) space, cybersecurity concerns were mentioned as the number one challenge to Industrial IoT adoption. Others see security risks as the second most important IIoT adoption challenge but does it really matter?
Cybersecurity is CRUCIAL everywhere in this digital economy and it certainly is a major challenge in IIoT as well. How else could it be?
Amidst the ongoing digital transformation initiatives in manufacturing, logistics, transportation, healthcare and other industries which are typically categorized under the Industrial Internet label, data breaches and all kids of cybercrime and cyberthreats are on the rise.
In the end, the IoT, also in the industrial context of Industry 4.0 is essentially about the movement to information-driven ecosystems of value. And when we talk about information, data and value, we inevitably talk growing risks as they are key assets and drivers of the industry.
The (re)design of security architectures in Industry 4.0
So, it’s not as if cybersecurity risks and cyberattacks are about to decrease, in general nor in industrial markets.
In our overview of digital transformation in healthcare, for instance, we saw how, according to IDC, by 2018 the number of ransomware attacks ALONE on healthcare organizations is poised to double (in one year!).
And, as we mentioned in our article on cybersecurity in the digital transformation economy, Gartner expects that over 20 percent of enterprise security attacks will involve IoT connections by 2020.
Looking at manufacturing, the major Internet of Things industry from an IoT spending perspective, IDC expects that by 2018, a proliferation of connected information, instrumentations, and decision cloud ecosystem networks will drive manufacturers to redesign their security architectures as you can read here.
The key thing is indeed to do something about it and that, among others, means embedded cybersecurity by design, end-to-end and in many cases redesigned.
The security challenges of IT/OT integration and the IIoT
One of the many challenges regarding security in the Industrial Internet of Things is that it’s different in some regards, with even more differences depending on the industry or use case.
Yet, in other regards the risks are very similar to those in consumer applications – and in an IT/OT context, operational teams will be exposed to the types of attacks that IT teams are used to seeing, as Robert Westervelt (IDC) puts it.
As Industrial companies pursue IIoT, it’s important to understand the new threats that can impact critical operations.

Greater connectivity with operational technology (OT) exposes operational teams to the types of attacks that IT teams are used to seeing, but with even higher stakes
(Robert Westervelt, security research manager at IDC)
The operational technologies driving manufacturing and other operations have until now lived in relatively splendid isolation. With the integration/convergence of IT (Information Technology) and OT (Operational Technology), which is essential for the Industrial Internet of Things this is changing, obviously with security challenges.
According to IDC only 20 percent of companies will be able to bypass cybersecurity issues and reach full IT/OT integration in 2017.
Other typical aspects of the Industrial Internet of Things include the increasing importance of fog computing or ‘the fog’ as Cisco calls it or edge computing, what it really is. You also find different connectivity solutions. There is the human element whereby access to assets, networks and IoT devices needs to be enforced with security policies. Endpoint security, software, the list goes on.
Industrial Internet Of Things security frameworks and new approaches
The industry does know about the cybersecurity challenges and risks regarding the Industrial Internet of Things, obviously.
There is a reason why the IIC (Industrial Internet Consortium) published an Industrial Internet Security Framework (IISF) in September 2016.
There is also more than one reason why fog computing exists and why the OpenFog Consortium doesn’t just focus on an open and interoperable infrastructure but also on secure information flows.
IDC expects that by 2019, at least 40 percent of IoT-created data will be stored, processed, analyzed and acted upon close to or at the edge of the network. On top of the benefits we tackled previously, this also has cybersecurity and industrial cybersecurity consequences.
IIoT: moving towards more complex applications with more advanced security technologies
It’s also not as if with the Industrial Internet all of the sudden every aspect of a factory is connected to the Internet as some seem to think.
What we see is a gradual move whereby immediate benefits are sought in areas such as maintenance, tracking, monitoring and services. As a matter of fact, in many plants, even in technology-intensive niches, the cloud, the Internet and to some extent the Internet of Things is just starting to be used for the optimization of industrial processes whereby the manufacturing process wouldn’t be endangered if there is no Internet or an attack.
Still, the market is evolving fast. We know the predictions, realities and efforts that are being made to boost the Industrial Internet and if cybersecurity is a concern, whether it’s number one or number ninety on the list, it needs to be addressed because it is not just a concern, it’s a reality.
Moreover, it’s becoming an ever bigger and more complex reality. That’s why companies are investing more in security IN the cloud and why the market for cybersecurity systems with cognitive and AI is growing as cybersecurity risks become too complex – and important.
According to IDC, by 2018, 70 percent of enterprise cybersecurity environments will use cognitive/AI technologies to assist humans in dealing with the vastly increasing scale and complexity of cyberthreats.
Cybersecurity and the Industrial Internet of Things: risk perceptions – and preparedness
Chief Information Security Officers, Chief Security Officers, CIOs and anyone professionally dealing with IT security knows that the stakes are high in the Industrial Internet of Things as well – and that the number of attacks will increase.
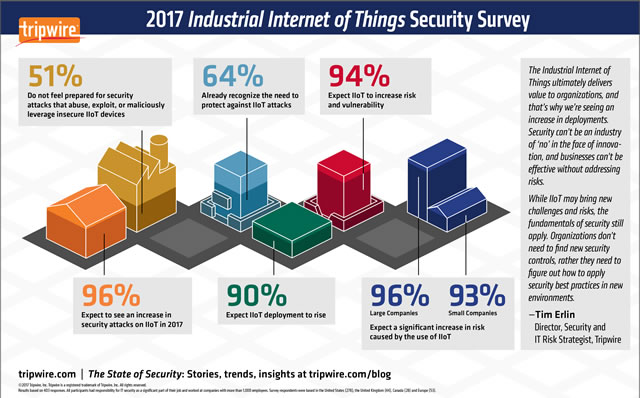
According to a January 2017 survey, released in March 2017 and conducted by Dimensional Research for Tripwire, a whopping 96 percent of them expect an increase of attacks on IIoT in 2017.
51 percent feels not prepared for attacks which exploit insecure IIoT devices (endpoint protection is one of the many topics in the mentioned 173-pages “Industrial Internet of Things Volume G4 Security Framework” by the IIC).
And the good news: 64 percent recognizes the need to take precautions against IIoT attacks as they become more popular.
Now the other 36 percent and time for action, for instance by downloading that IIC framework (PDF opens).
Top image: Shutterstock – Copyright: wk1003mike – All other images are the property of their respective mentioned owners.

